A cross platform, customizable graphical frontend for launching emulators and managing your game collection.
A cross platform, customizable graphical frontend for launching emulators and managing your game collection.
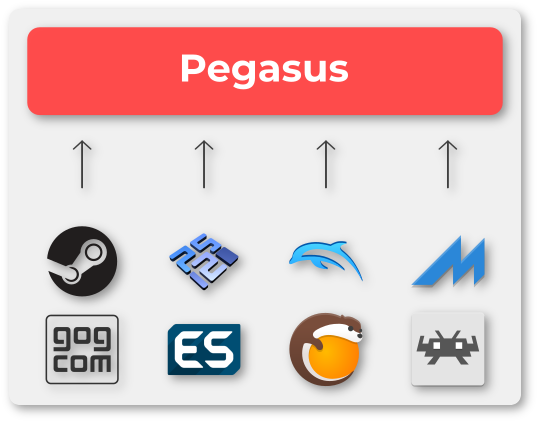
Pegasus is a graphical frontend for browsing your game library (especially retro games) and launching them from one place. It's focusing on customizability, cross platform support (including embedded devices) and high performance.
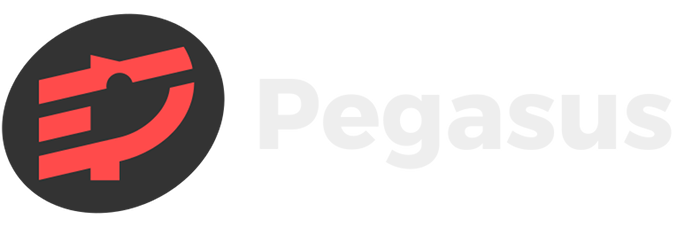
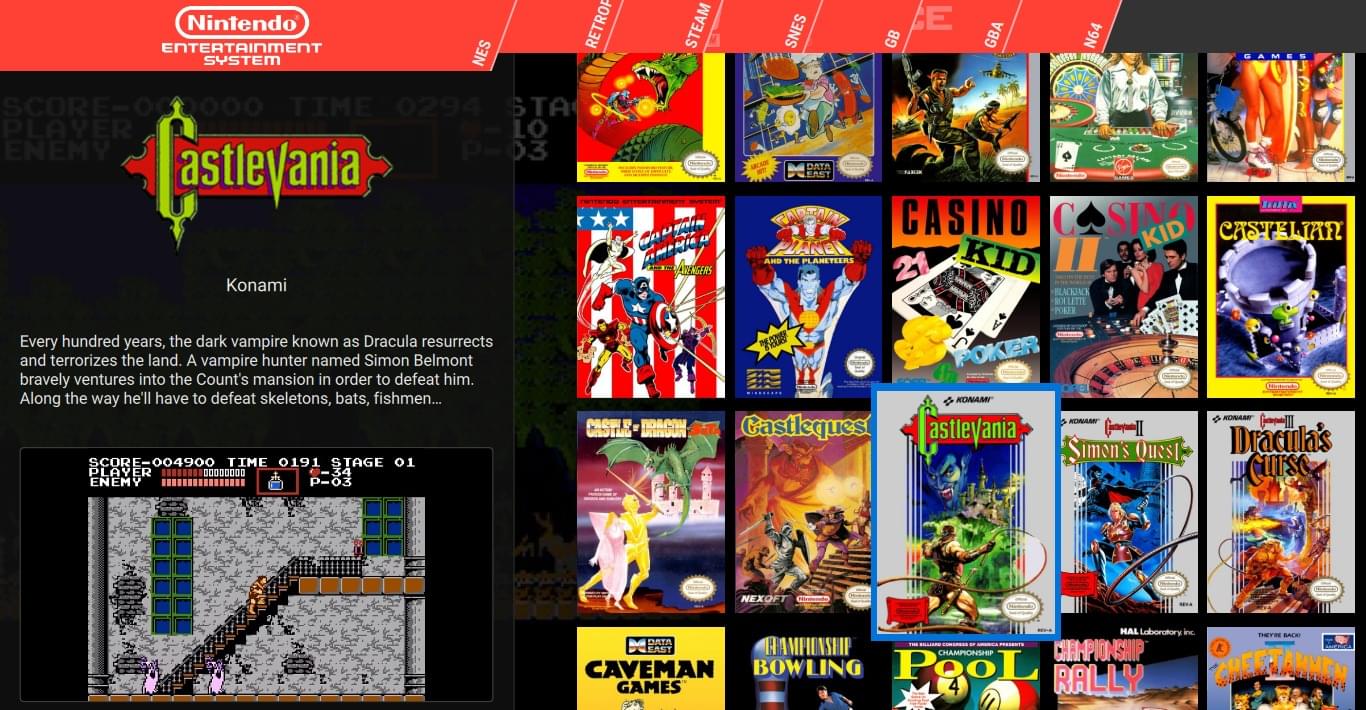
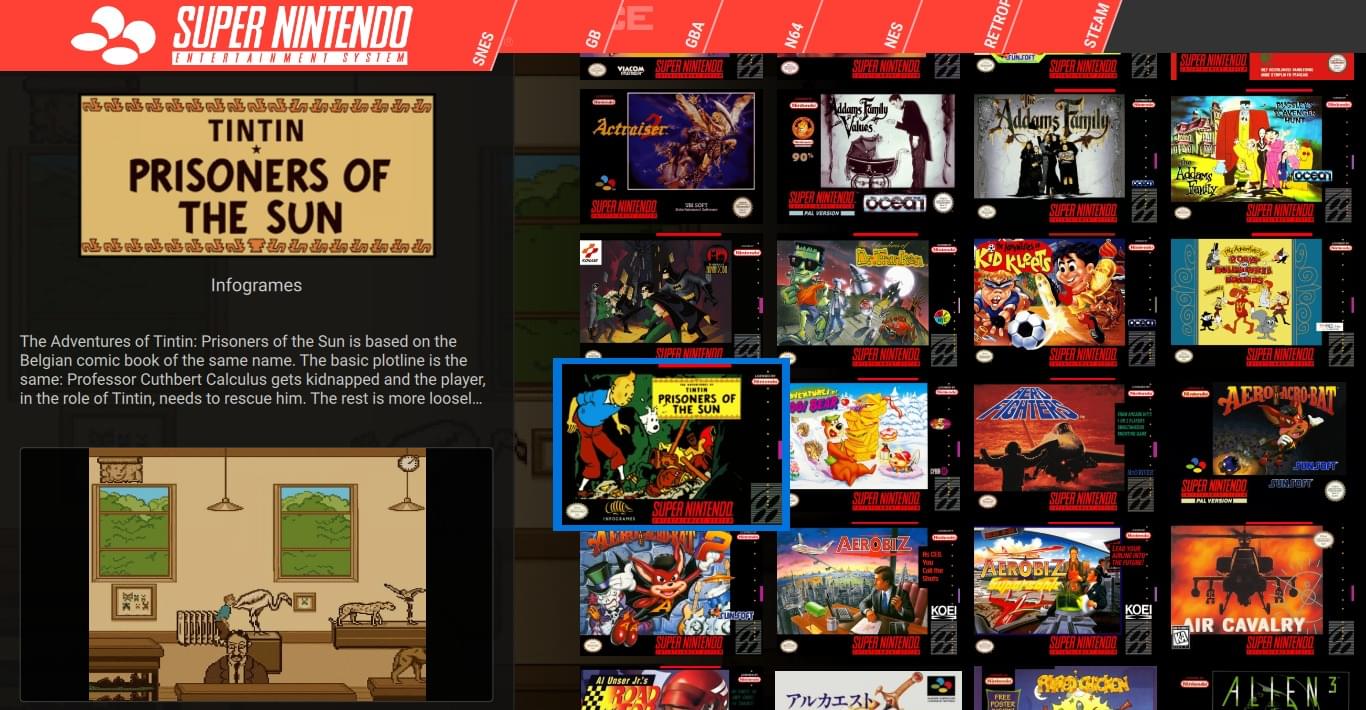
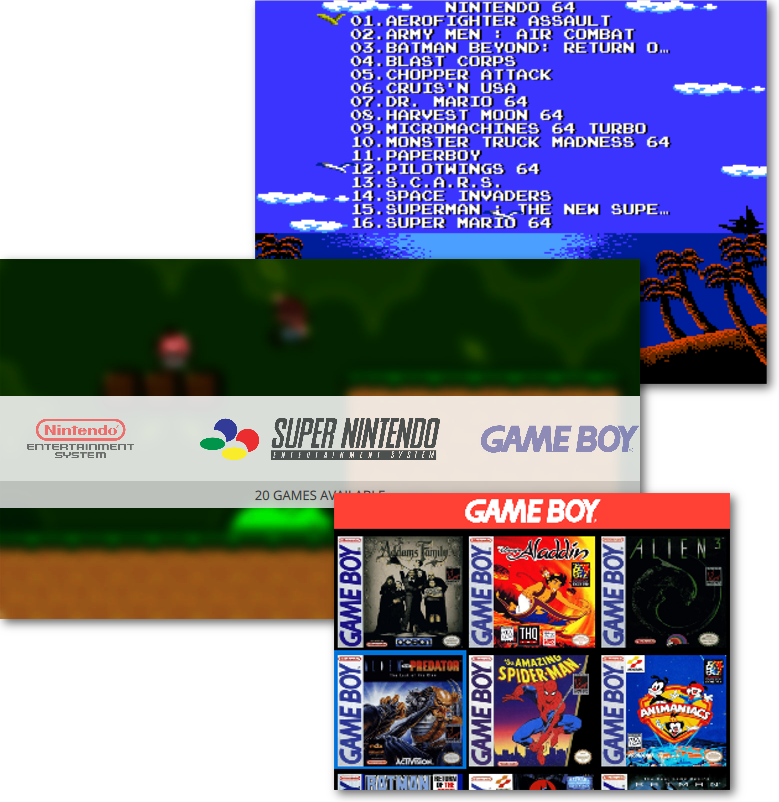
Instead of launching different games with different emulators one by one manually, you can add them to Pegasus and launch the games from a friendly graphical screen from your couch. You can add all kinds of artworks, metadata or video previews for each game to make it look even better!
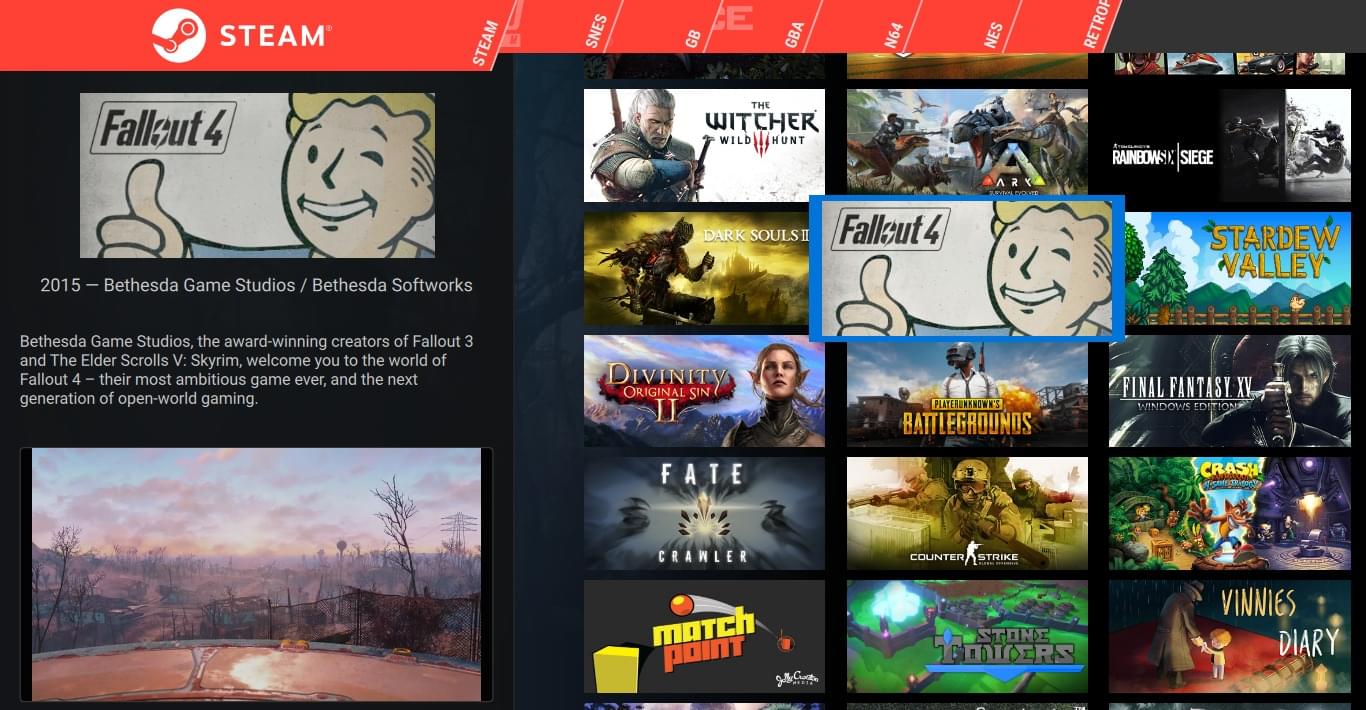
With additional themes, you can completely change everything that is on the screen. Add or remove UI elements, menu screens, whatever. Want to make it look like Kodi? Steam? Any other launcher? No problem. You can add animations and effects, 3D scenes, or even run your custom shader code.
Pegasus can run on Linux, Windows, Mac, Raspberry Pi, Odroid and Android devices. It's compatible with EmulationStation metadata and gamelist files, and instantly recognizes your Steam games!
In conclusion, while the allure of a free, powerful technical tool is strong, the cost of a compromised system far outweighs the price of a legitimate license. Protecting your digital integrity requires vigilance and a commitment to using only trusted, verified software solutions.
Only download software from the developer’s official website or recognized app stores. In conclusion, while the allure of a free,
Using your computer’s processing power to launch cyberattacks on others without your knowledge. Technical and Legal Consequences while the allure of a free
Below is an essay on the importance of software security and the risks associated with downloading unverified technical tools. The Hidden Risks of Unverified Technical Tools powerful technical tool is strong
Recording your keystrokes to steal passwords and financial information.
Encrypting your files and demanding payment for their release.