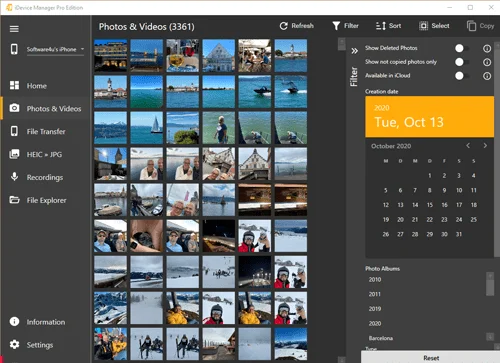
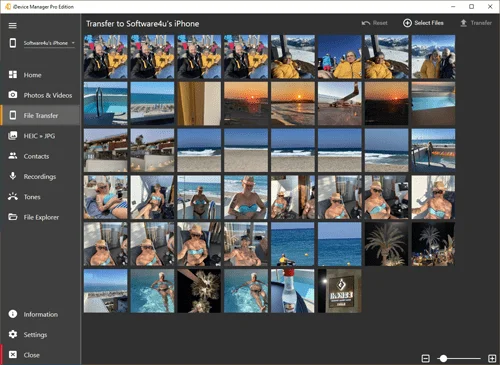
📸 Copy iPhone photos to PC – free up storage space with just one click
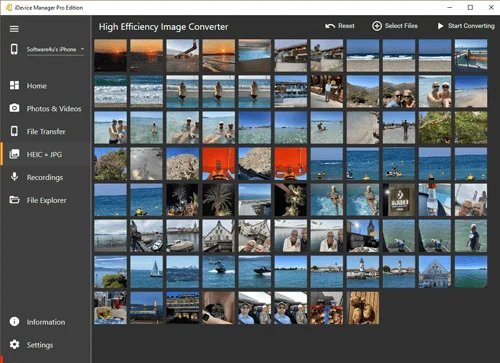
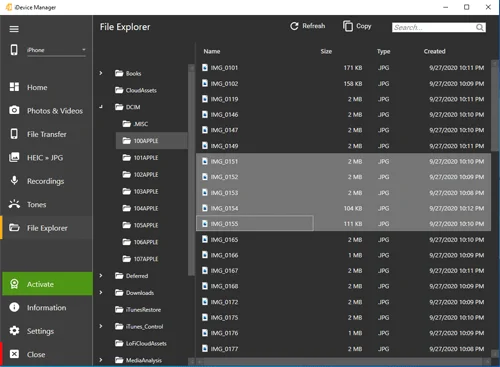
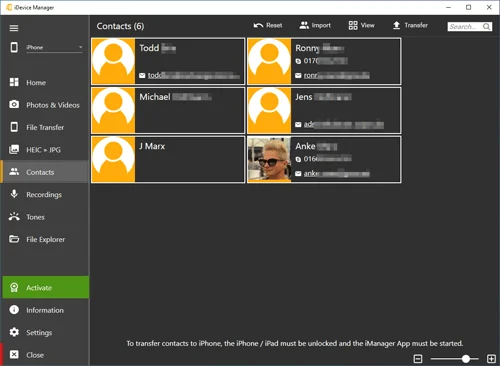
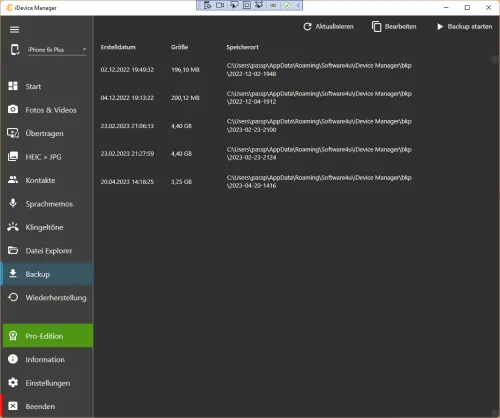
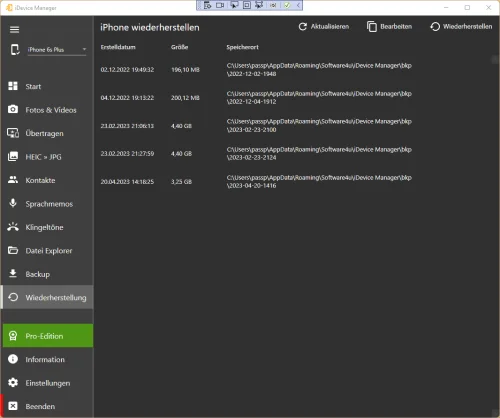
With iDevice Manager, you can save iPhone photos to your PC, organize them, and back them up – without iTunes or iCloud. Whether it's vacation photos, screenshots, or videos, you can transfer your files directly to your computer without any loss of quality.
- Transfer multiple photos or entire albums at once
- Automatic detection of new images
- No loss of quality or compression
- Secure backups of your memories with one click
👉 Tip: Save storage space on your iPhone – back up your favorite images permanently on your PC!
Transfer iPhone photos & videos to PC – easily, quickly, and without iTunes (Windows 10/11)